![CrowdStrike + Fortinet + Active Directory + D3 Smart SOAR] Spearphishing Attachment - T1566.001 - YouTube CrowdStrike + Fortinet + Active Directory + D3 Smart SOAR] Spearphishing Attachment - T1566.001 - YouTube](https://i.ytimg.com/vi/UNa-vfrgVXs/sddefault.jpg)
CrowdStrike + Fortinet + Active Directory + D3 Smart SOAR] Spearphishing Attachment - T1566.001 - YouTube

Automatically Triage and Respond to Mimikatz Alerts with CrowdStrike, Okta, and Smart SOAR | D3 Security

CrowdStrike Falcon Platform Detects and Prevents Active Intrusion Campaign Targeting 3CXDesktopApp Customers - cost solution for cybersecurity in Ukraine from IIT Distribution

Adversaries Can “Log In with Microsoft” through the nOAuth Azure Active Directory Vulnerability - cost solution for cybersecurity in Ukraine from IIT Distribution

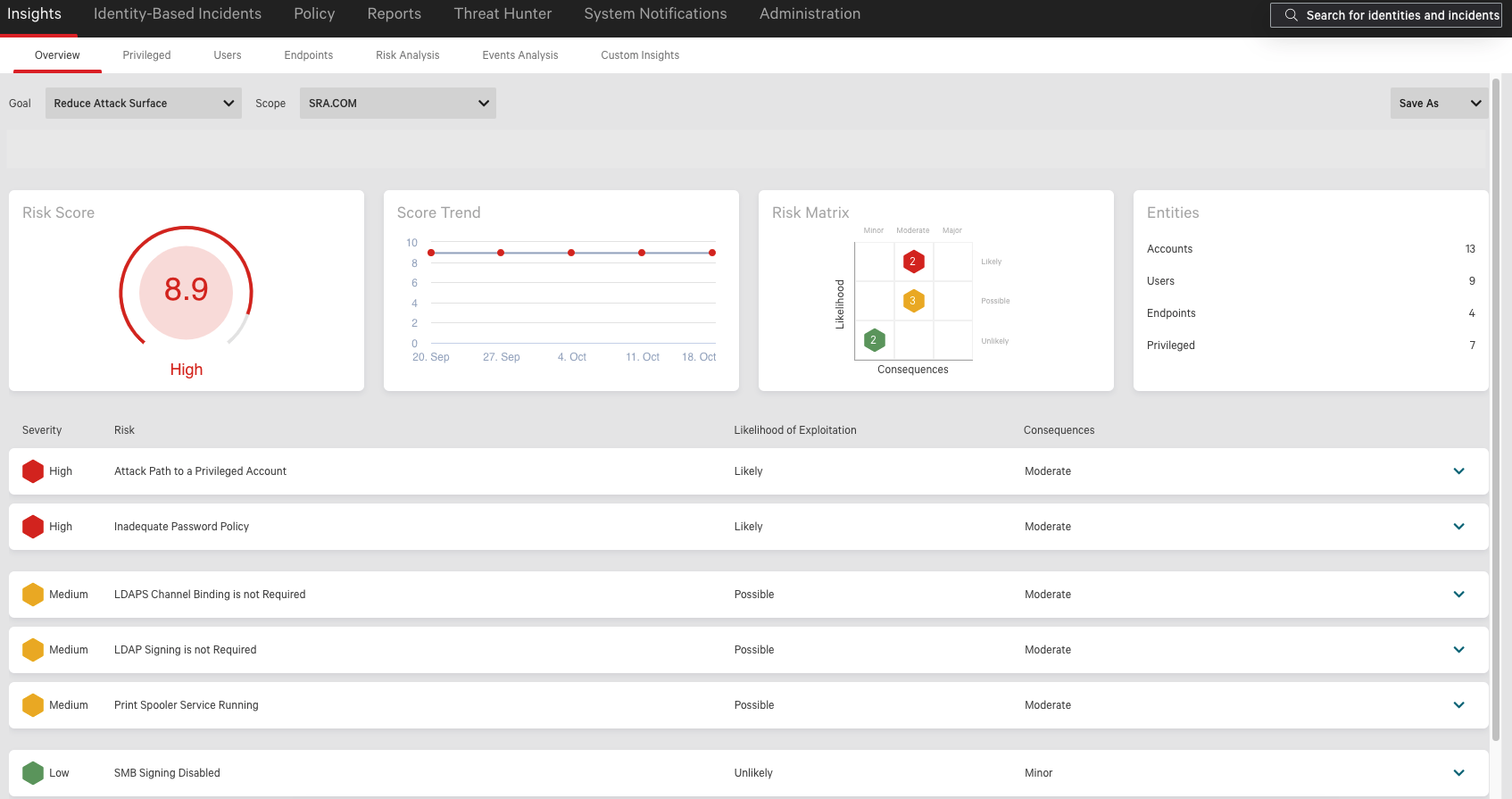
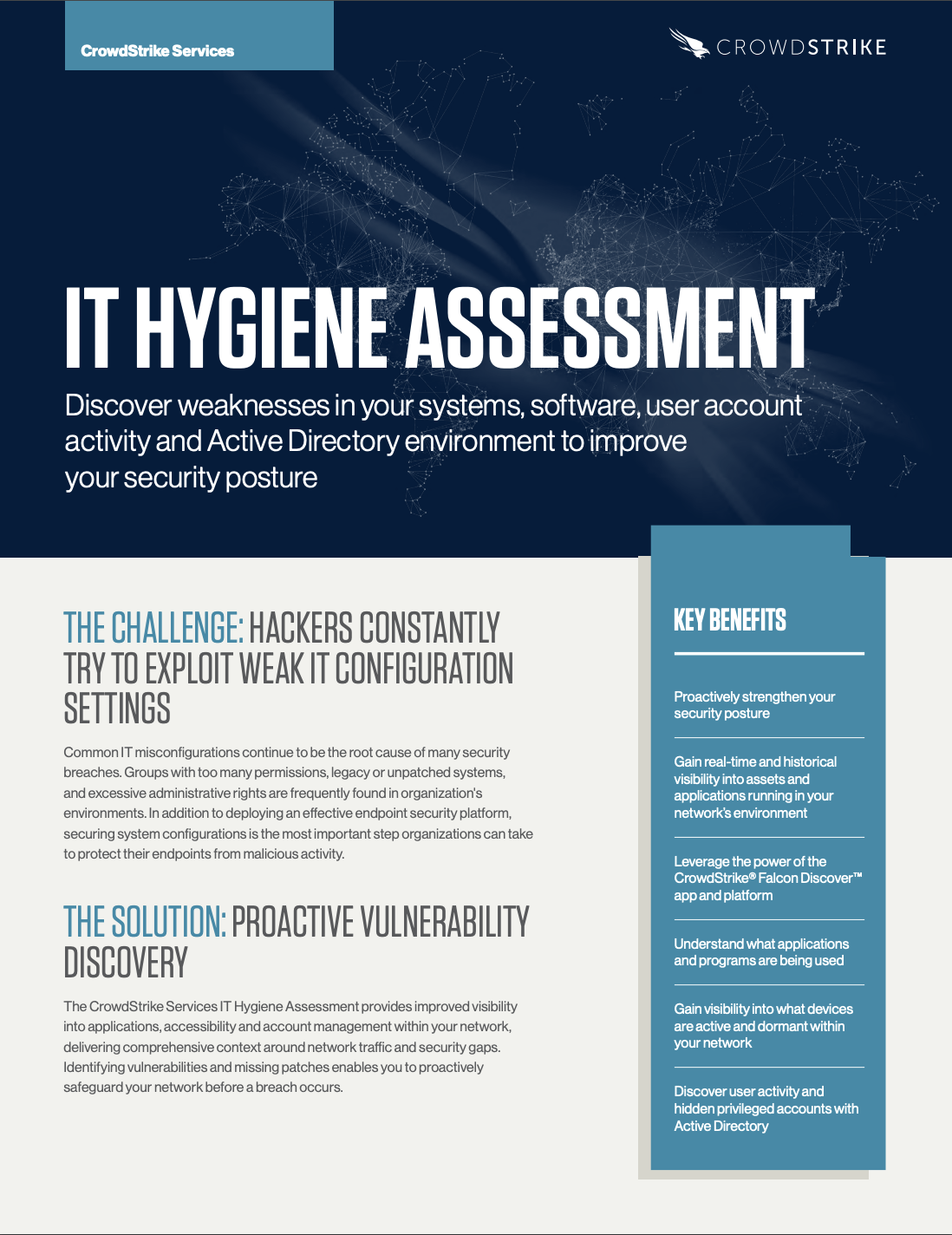
CrowdStrike's complimentary Active Directory Risk Review helped an insurance company find more than 20 accounts with SPNs and compromised passwords.... | By CrowdStrike | Facebook

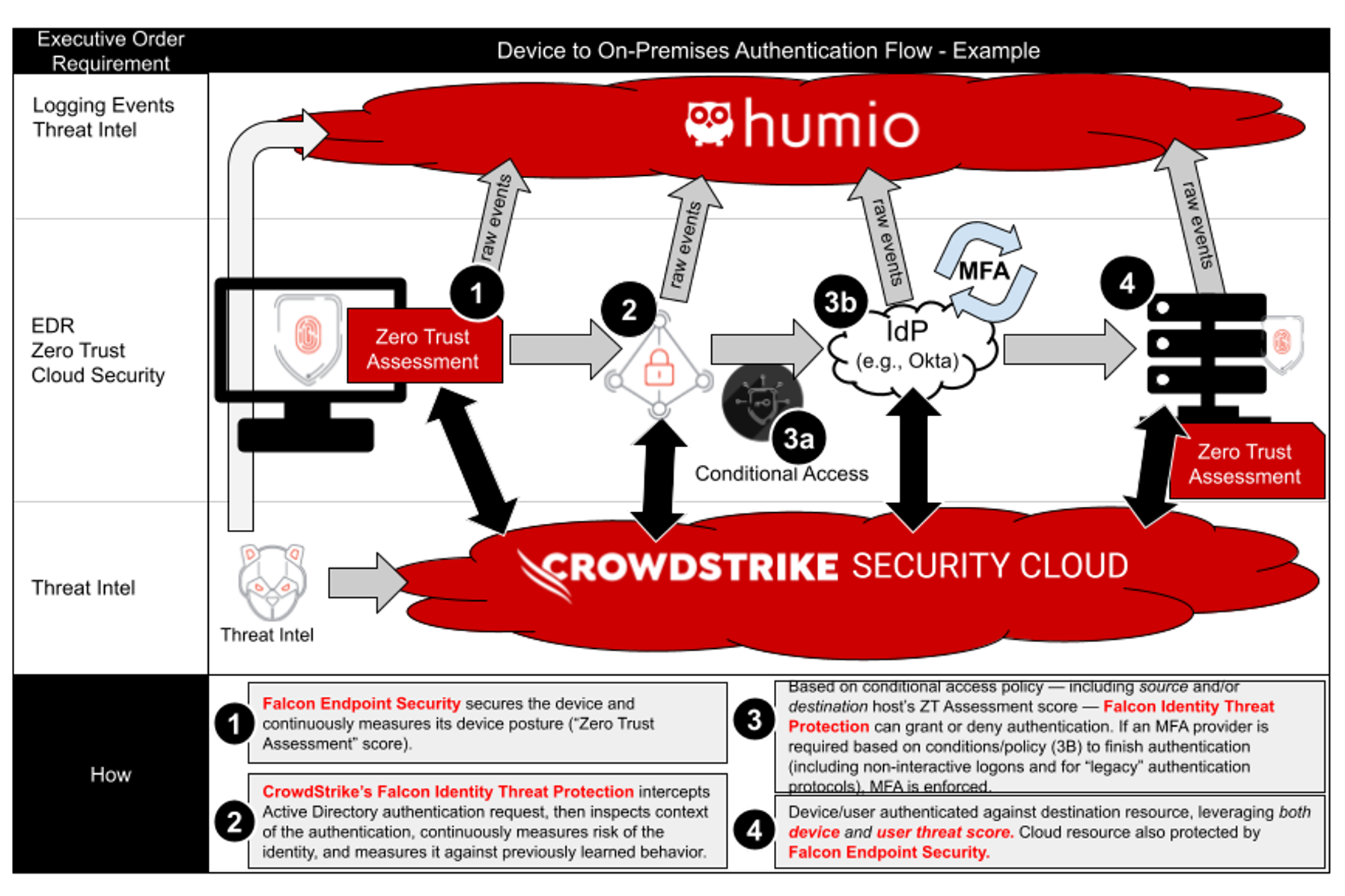
Securing private applications with CrowdStrike Zero Trust Assessment and AWS Verified Access - crowdstrike.com







![CrowdStrike + Zscaler + Active Directory + Smart SOAR] Cross-Stack Analysis - YouTube CrowdStrike + Zscaler + Active Directory + Smart SOAR] Cross-Stack Analysis - YouTube](https://i.ytimg.com/vi/4CI8_3NTGTA/maxresdefault.jpg)