Observations from a Log4j Decoy: From Vulnerability to Infection to DDOS in Record Time - Fidelis Security

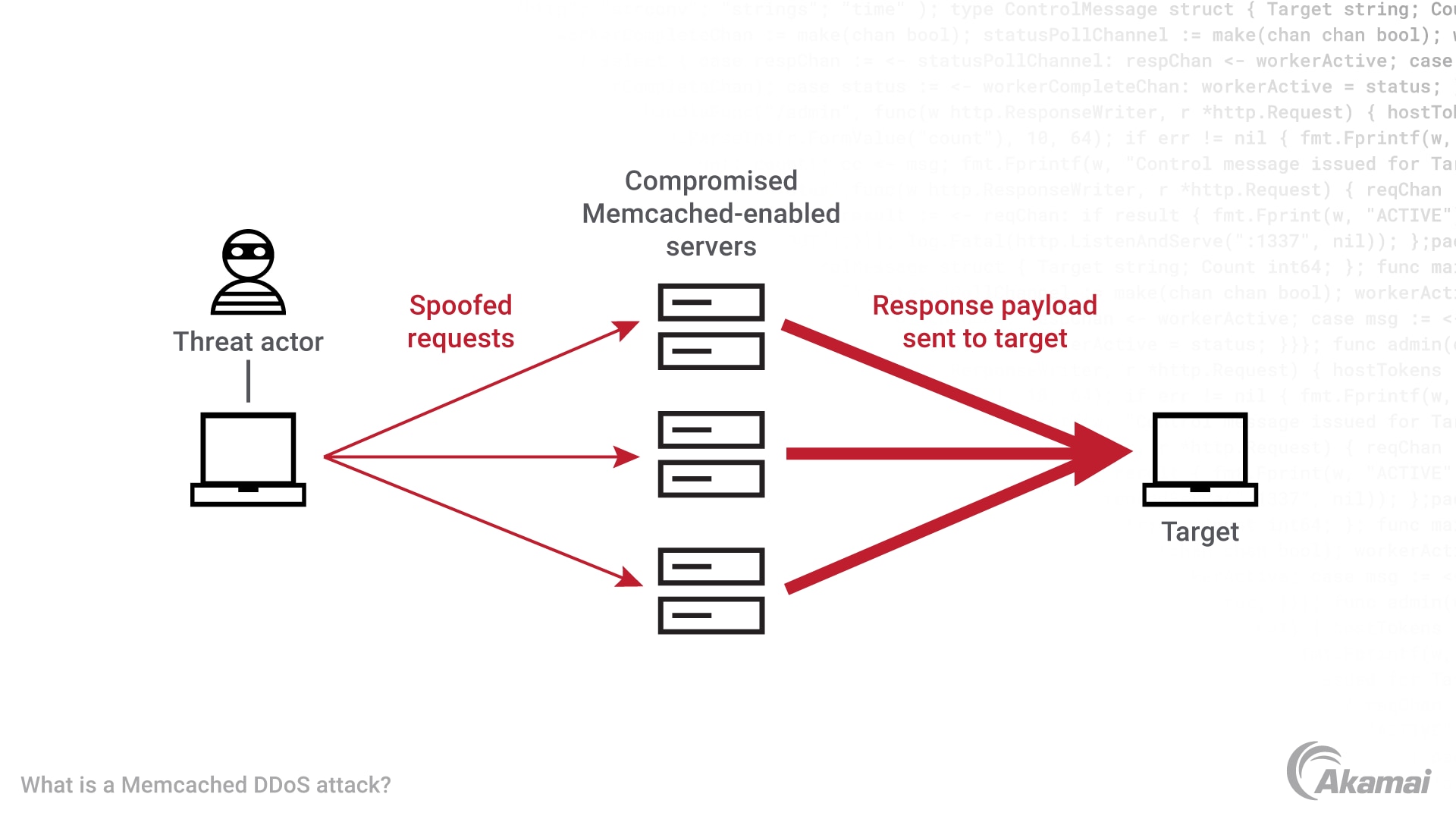
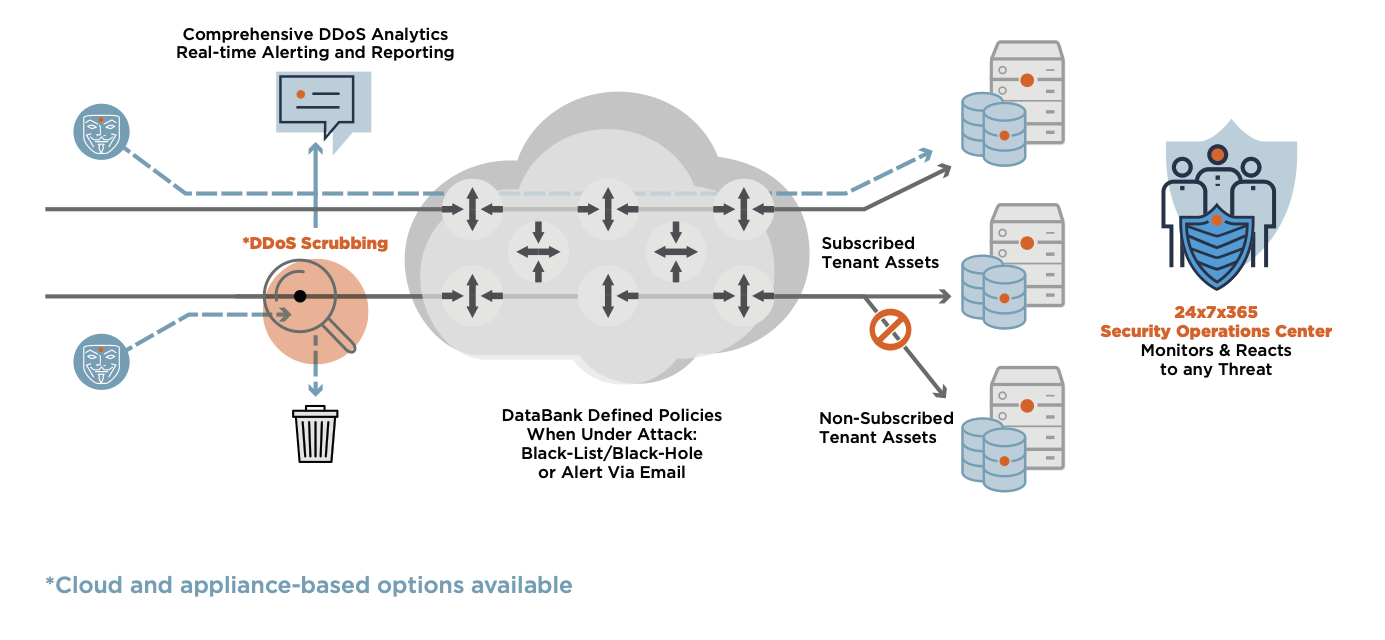
1TB Multi-Vector DDoS Attack in LATAM Blocked after CVE-2022-26143 Vulnerability Exploited - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.